Encrypt data in transit
Big picture
Enable WireGuard to secure on the wire in-cluster pod traffic in a Calico Cloud cluster.
Value
When this feature is enabled, Calico Cloud automatically creates and manages WireGuard tunnels between nodes providing transport-level security for inter-node, in-cluster pod traffic. WireGuard provides formally verified secure and performant tunnels without any specialized hardware. For a deep dive in to WireGuard implementation, see this white paper.
Calico Cloud supports WireGuard encryption for both IPv4 and IPv6 traffic. These can be independently enabled in the FelixConfiguration resource: wireguardEnabled
enables encrypting IPv4 traffic over an IPv4 underlay network and wireguardEnabledV6 enables encrypting IPv6 traffic over an IPv6 underlay network.
Before you begin
Terminology
- Inter-node pod traffic: Traffic leaving a pod from one node destined to a pod on another node
- Inter-node, host-network traffic: traffic generated by the node itself or a host-networked-pod destined to another node or host-networked-pod
- Same-node pod traffic: Traffic between pods on the same node
Supported encryption
- Inter-node pod traffic: IPv4 only
- Inter-node, host-network traffic, IPv4/IPv6: supported only on managed clusters deployed on EKS and AKS
Unsupported
- Encrypted same-node pod traffic
- GKE
- Using your own custom keys to encrypt traffic
Required
-
On all nodes in the cluster that you want to participate in Calico Cloud encryption, verify that the operating system(s) on the nodes are installed with WireGuard.
noteSome node operating systems do not support WireGuard, or do not have it installed by default. Enabling Calico Cloud WireGuard encryption does not require all nodes to be installed with WireGuard. However, traffic to or from a node that does not have WireGuard installed, will not be encrypted.
-
IP addresses for every node in the cluster. This is required to establish secure tunnels between the nodes. Calico Cloud can automatically do this using IP autodetection methods.
How to
- Install WireGuard
- Enable WireGuard for a cluster
- Verify encryption is enabled
- Disable WireGuard for an individual node
- Disable WireGuard for a cluster
Install WireGuard
WireGuard is included in Linux 5.6+ kernels, and has been backported to earlier Linux kernels in some Linux distributions.
Install WireGuard on cluster nodes using instructions for your operating system. Note that you may need to reboot your nodes after installing WireGuard to make the kernel modules available on your system.
Use the following instructions for these platforms that are not listed on the WireGuard installation page, before proceeding to enabling WireGuard.
- EKS
- AKS
- OpenShift
To install WireGuard on the default Amazon Machine Image (AMI):
sudo yum install kernel-devel-`uname -r` -y
sudo yum install https://dl.fedoraproject.org/pub/epel/epel-release-latest-7.noarch.rpm -y
sudo curl -o /etc/yum.repos.d/jdoss-wireguard-epel-7.repo https://copr.fedorainfracloud.org/coprs/jdoss/wireguard/repo/epel-7/jdoss-wireguard-epel-7.repo
sudo yum install wireguard-dkms wireguard-tools -y
AKS cluster nodes run Ubuntu with a kernel that has WireGuard installed already, so there is no manual installation required.
To install WireGuard for OpenShift v4.8:
-
Install requirements:
-
Download and configure the tools needed for kmods.
FAKEROOT=$(mktemp -d)
git clone https://github.com/tigera/kmods-via-containers
cd kmods-via-containers
make install FAKEROOT=${FAKEROOT}
cd ..
git clone https://github.com/tigera/kvc-wireguard-kmod
cd kvc-wireguard-kmod
make install FAKEROOT=${FAKEROOT}
cd ..
-
Configure/edit
${FAKEROOT}/root/etc/kvc/wireguard-kmod.conf.a. You must then set the URLs for the
KERNEL_CORE_RPM,KERNEL_DEVEL_RPMandKERNEL_MODULES_RPMpackages in the conf file$FAKEROOT/etc/kvc/wireguard-kmod.conf. Obtain copies forkernel-core,kernel-devel, andkernel-modulesrpms from RedHat Access and host it in an http file server that is reachable by your OCP workers.b. For help configuring
kvc-wireguard-kmod/wireguard-kmod.confand WireGuard version to kernel version compatibility, see the kvc-wireguard-kmod README file. -
Get RHEL Entitlement data from your own RHEL8 system from a host in your cluster.
tar -czf subs.tar.gz /etc/pki/entitlement/ /etc/rhsm/ /etc/yum.repos.d/redhat.repo -
Copy the
subs.tar.gzfile to your workspace and then extract the contents using the following command.tar -x -C ${FAKEROOT}/root -f subs.tar.gz -
Transpile your machine config using CoreOS Butane.
cd kvc-wireguard-kmodmake ignition FAKEROOT=${FAKEROOT} > mc-wg.yaml -
With the KUBECONFIG set for your cluster, run the following command to apply the MachineConfig which will install WireGuard across your cluster.
oc create -f mc-wg.yaml
Enable WireGuard for a cluster
Enable IPv4 WireGuard encryption across all the nodes using the following command.
kubectl patch felixconfiguration default --type='merge' -p '{"spec":{"wireguardEnabled":true}}'
Enable IPv6 WireGuard encryption across all the nodes using the following command.
kubectl patch felixconfiguration default --type='merge' -p '{"spec":{"wireguardEnabledV6":true}}'
To enable both IPv4 and IPv6 WireGuard encryption across all the nodes, use the following command.
kubectl patch felixconfiguration default --type='merge' -p '{"spec":{"wireguardEnabled":true,"wireguardEnabledV6":true}}'
The above command can be used to change other WireGuard attributes. For a list of other WireGuard parameters and configuration evaluation, see the Felix configuration.
We recommend that you review and modify the MTU used by Calico Cloud networking when WireGuard is enabled to increase network performance. Follow the instructions in the Configure MTU to maximize network performance guide to set the MTU to a value appropriate for your network.
Verify encryption is enabled
To verify that the nodes are configured for WireGuard encryption, check the node status set by Felix using kubectl. For example:
kubectl get node <NODE-NAME> -o yaml
...
kind: Node
metadata:
annotations:
projectcalico.org/WireguardPublicKey: jlkVyQYooZYzI2wFfNhSZez5eWh44yfq1wKVjLvSXgY=
...
Enable WireGuard statistics
Since v3.11.1, WireGuard statistics are now automatically enabled with the enable WireGuard setting(s) mentioned above.
View WireGuard statistics
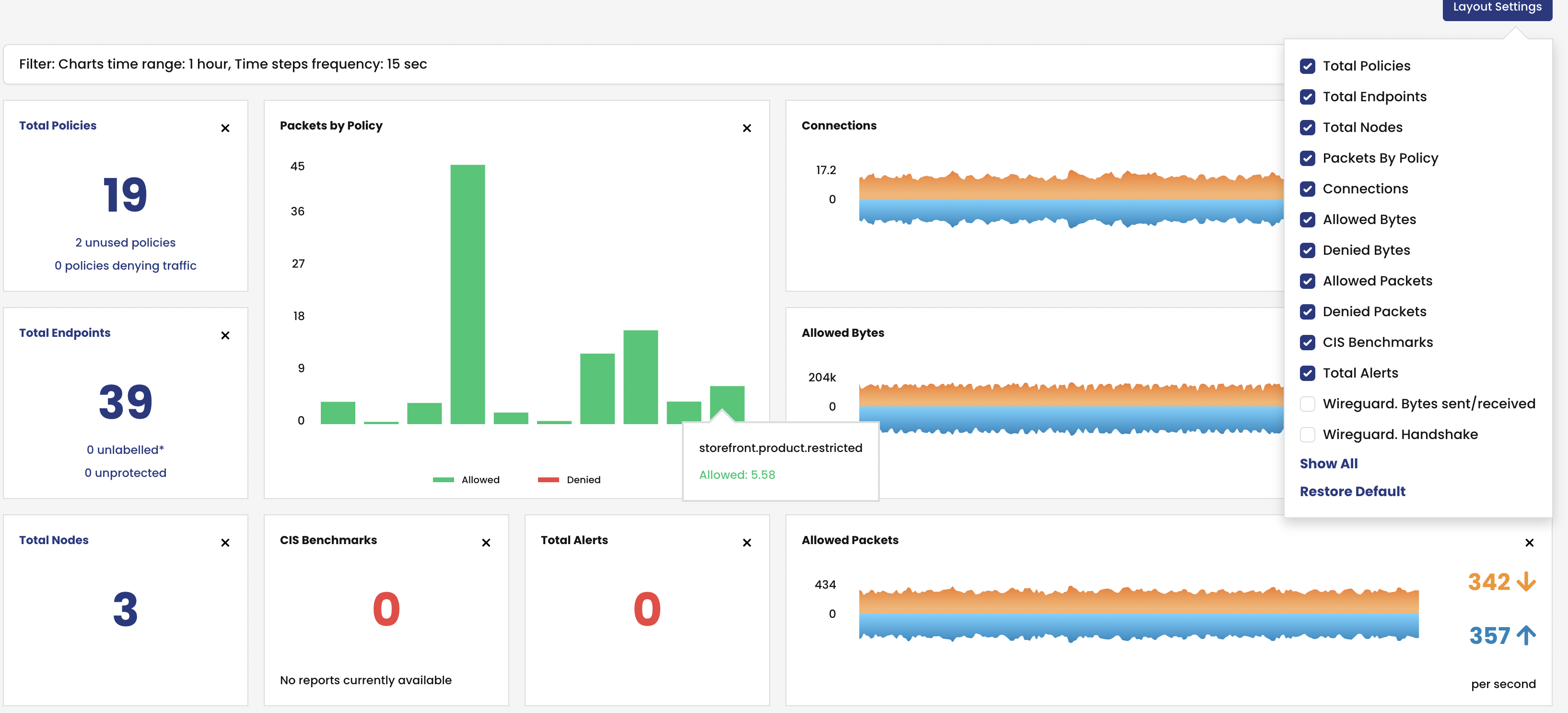
To view WireGuard statistics in the web console, you must enable them. From the left navbar, click Dashboard, and the Layout Settings icon.
Disable WireGuard for an individual node
To disable WireGuard on a specific node with WireGuard installed, modify the node-specific Felix configuration. e.g., to turn off encryption for pod traffic on node my-node, use the following command. This command disables WireGuard for both IPv4 and IPv6, modify it accordingly if disabling only either IP version:
cat <<EOF | kubectl apply -f -
apiVersion: projectcalico.org/v3
kind: FelixConfiguration
metadata:
name: node.my-node
spec:
logSeverityScreen: Info
reportingInterval: 0s
wireguardEnabled: false
wireguardEnabledV6: false
EOF
With the above command, Calico will not encrypt any of the pod traffic to or from node my-node.
To enable encryption for IPv4 and IPv6 pod traffic on node my-node again, patch this node's FelixConfiguration (modify accordingly if only dealing with IPv4 or IPv6):
kubectl patch felixconfiguration node.my-node --type='merge' -p '{"spec":{"wireguardEnabled":true,"wireguardEnabledV6":true}}'
Disable WireGuard for a cluster
To disable WireGuard on all nodes modify the default Felix configuration. For example:
kubectl patch felixconfiguration default --type='merge' -p '{"spec":{"wireguardEnabled":false,"wireguardEnabledV6":false}}'